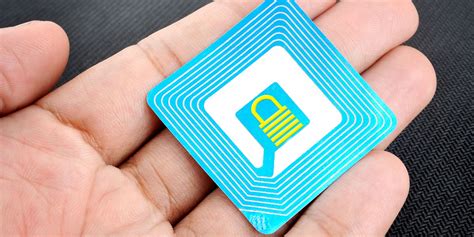
can the rfid tag locked by unauthorized user Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
Visit ESPN for the complete 2024 NFL season Playoff standings. Includes winning percentage, home and away record, and current streak. . Wins tie break over Carolina based .
0 · rfid security update
1 · rfid security
2 · rfid attacks
3 · is rfid safe to hack
4 · how to protect sensitive rfid
5 · how to protect against rfid
6 · how rfid can be hacked
7 · can rfid be blocked
The service marks the first time consumers can purchase an NFC-enabled mobile device off the shelf and use that device to make Visa payWave-enabled transactions at the .
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement . RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement authentication mechanisms to ensure that only authorized tags and readers can interact with each other.
5. Lock password. A lock password is a 32-bit password which must be transmitted before a tag will transmit its data. Skimmers will be unable to access the data since they can’t provide the password (a 32-bit password has 4,294,967,296 possible combinations).Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.Eavesdropping is a technique used by attackers to intercept and decode the radio signals exchanged between RFID tags and readers. By capturing these signals, hackers can gain unauthorized access to sensitive information, such as personal identification numbers or confidential data.
Once an attacker has copied the information from the victim’s RFID card, they can clone it on to a blank RFID card for use at your facility. When employees are in the office, it is generally preferred that they wear their RFID card out in .An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks. User consent and transparency becomes crucial when a tag has a unique serial number and can be associated to a consumer. It is recommended for RFID users to take steps to secure their data by locking memory banks. Eavesdropping: RFID signals can be intercepted by unauthorized individuals, allowing them to eavesdrop on the communication between tags and readers. This can lead to the theft of sensitive information, such as personal data or intellectual property.
Abstract—Many RFID tags store valuable information privy to their users that can easily be subject to unauthorized reading, leading to owner tracking or impersonation.
rfid security update

RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement authentication mechanisms to ensure that only authorized tags and readers can interact with each other.
massachusetts covid smart health card
5. Lock password. A lock password is a 32-bit password which must be transmitted before a tag will transmit its data. Skimmers will be unable to access the data since they can’t provide the password (a 32-bit password has 4,294,967,296 possible combinations).Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.Eavesdropping is a technique used by attackers to intercept and decode the radio signals exchanged between RFID tags and readers. By capturing these signals, hackers can gain unauthorized access to sensitive information, such as personal identification numbers or confidential data.
Once an attacker has copied the information from the victim’s RFID card, they can clone it on to a blank RFID card for use at your facility. When employees are in the office, it is generally preferred that they wear their RFID card out in .An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks. User consent and transparency becomes crucial when a tag has a unique serial number and can be associated to a consumer. It is recommended for RFID users to take steps to secure their data by locking memory banks.
rfid security
Eavesdropping: RFID signals can be intercepted by unauthorized individuals, allowing them to eavesdrop on the communication between tags and readers. This can lead to the theft of sensitive information, such as personal data or intellectual property.

rfid attacks

mac os remove smart card certifcaties
mac not reading smart card
Take the blank MIFARE Classic card and place it near your phone. In the app, select the write option. In the menu, select the Write Dump (clone) option. Select the dump you got from the previous .Most of the time these NFC cards are using encryption so it is not possible to emulate them .
can the rfid tag locked by unauthorized user|can rfid be blocked