can you hijack a smart card authenticated sessions The web server sends the token to the client browser after the client has been authenticated. Through session hijacking, attackers can intercept, predict, or brute-force a . Highly collectible 3D printable NFC tokens for use with Nintendo video game consoles. Designs for all 91 amiibos in the Smash Bros. series. .Shop for SIM cards for as low . as $0 today. The SIM stores your account information and connects your device to the T‑Mobile network. Your phone may have two options for SIM cards, a digital eSIM or a Physical SIM card. Please select one of the following to continue bringing .
0 · session hijacking url
1 · session hijacking
2 · ping session hijacking
Newson's Electronics is reducing e-waste one repair at a time!If you want to support my channel please check out my other listings. Books by the authorHEART .My College decided to switch to using NFC card entry to the buildings instead if the old swipe entry. Unfortunately, the new cards appear to contain the world's worst NFC chip that only .
In short: Stealing live sessions enables attackers to bypass authentication controls like MFA. If you can hijack an existing session, you have fewer steps to worry about – no messing about with converting stolen usernames and passwords into an authenticated session.
The web server sends the token to the client browser after the client has been authenticated. Through session hijacking, attackers can intercept, predict, or brute-force a .
The overall hack can be summarized like this: If I can steal the subject label attached to your authentication method, I might be able to steal your identity even if you use .
A session hijacking attack happens when an attacker takes over your internet session — for instance, while you’re checking your credit card balance, paying your bills, or .
This article will detail the top six techniques for attacking 2FA and present you with an all-around picture for the kind of 2FA attackers you can expect to encounter when working .
If the attacker gets that key, they can hijack the authentication process right at the source. This vulnerability has been dubbed the “golden SAML method” because no one has . A cybercriminal can hijack the session of the victim by stealing the session ID or a session cookie to make the server believe that the criminal is the legitimate user. The bad guys can also hijack the session by persuading the . Man-in-the-middle: Also known as session hijacking or real-time phishing, this attack involves threat actors establishing a fake authentication webpage to trick users into entering .In a session token hijacking attack, the attacker intercepts the session token, allowing them to impersonate the legitimate user. This unauthorized access can lead to significant .
In short: Stealing live sessions enables attackers to bypass authentication controls like MFA. If you can hijack an existing session, you have fewer steps to worry about – no messing about with converting stolen usernames and passwords into an authenticated session. The Grand Finale: Hijacking Smart Cards. Smart card redirection also uses the RDPDR channel; it is just another device. This means that if a user connects using a smart card (or just redirects their smart card to use it from within the session), the attacker could also take over the user’s smart card and use it as if it were connected to . The web server sends the token to the client browser after the client has been authenticated. Through session hijacking, attackers can intercept, predict, or brute-force a legitimate session token in order to pose as the authenticated .
The overall hack can be summarized like this: If I can steal the subject label attached to your authentication method, I might be able to steal your identity even if you use otherwise very. A session hijacking attack happens when an attacker takes over your internet session — for instance, while you’re checking your credit card balance, paying your bills, or shopping at an online store. Session hijackers usually target browser or web application sessions. This article will detail the top six techniques for attacking 2FA and present you with an all-around picture for the kind of 2FA attackers you can expect to encounter when working as an ethical hacker. If the attacker gets that key, they can hijack the authentication process right at the source. This vulnerability has been dubbed the “golden SAML method” because no one has yet figured out an effective way to remove this threat.
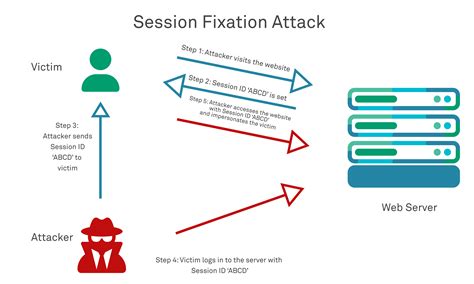
A cybercriminal can hijack the session of the victim by stealing the session ID or a session cookie to make the server believe that the criminal is the legitimate user. The bad guys can also hijack the session by persuading the victim to log in using a compromised session ID.
how to use nfc tags with iphone
Man-in-the-middle: Also known as session hijacking or real-time phishing, this attack involves threat actors establishing a fake authentication webpage to trick users into entering their credentials.
In a session token hijacking attack, the attacker intercepts the session token, allowing them to impersonate the legitimate user. This unauthorized access can lead to significant consequences, including identity theft and breaches of confidential communications. In short: Stealing live sessions enables attackers to bypass authentication controls like MFA. If you can hijack an existing session, you have fewer steps to worry about – no messing about with converting stolen usernames and passwords into an authenticated session.
session hijacking url
The Grand Finale: Hijacking Smart Cards. Smart card redirection also uses the RDPDR channel; it is just another device. This means that if a user connects using a smart card (or just redirects their smart card to use it from within the session), the attacker could also take over the user’s smart card and use it as if it were connected to . The web server sends the token to the client browser after the client has been authenticated. Through session hijacking, attackers can intercept, predict, or brute-force a legitimate session token in order to pose as the authenticated . The overall hack can be summarized like this: If I can steal the subject label attached to your authentication method, I might be able to steal your identity even if you use otherwise very.
A session hijacking attack happens when an attacker takes over your internet session — for instance, while you’re checking your credit card balance, paying your bills, or shopping at an online store. Session hijackers usually target browser or web application sessions. This article will detail the top six techniques for attacking 2FA and present you with an all-around picture for the kind of 2FA attackers you can expect to encounter when working as an ethical hacker. If the attacker gets that key, they can hijack the authentication process right at the source. This vulnerability has been dubbed the “golden SAML method” because no one has yet figured out an effective way to remove this threat. A cybercriminal can hijack the session of the victim by stealing the session ID or a session cookie to make the server believe that the criminal is the legitimate user. The bad guys can also hijack the session by persuading the victim to log in using a compromised session ID.
Man-in-the-middle: Also known as session hijacking or real-time phishing, this attack involves threat actors establishing a fake authentication webpage to trick users into entering their credentials.
session hijacking
ping session hijacking
View the Box Score for the NFL football game between the Green Bay Packers and the San Francisco 49ers on January 3, 1999. . 1998 NFC Wild Card Game Green Bay .1998–99 NFL playoffs; Dates: January 2–31, 1999: Season: 1998: Teams: 12: . the third-seeded division winner hosted the sixth seed wild card, and the fourth seed hosted the fifth. The 1 and 2 seeds from each conference received a first . This was the first NFC Championship Game to go to overtime (since, there . See more
can you hijack a smart card authenticated sessions|ping session hijacking