ssh smart card device Connecting using public key in SSH requires the presence of the public key on the server to verify clients signatures. If we don't have the public key stored separately in PEM format, we . See more 2019 GOODYEAR COTTON BOWL CLASSIC on NEWSRADIO 790WAEB! Saturday, December 28, 2019 at 12noon - Broadcasting Show starts at 10:30am. On your radio - 790 WAEB-AM. On WAEB's FREE iHeartradio .
0 · Smart card authentication with SSH
1 · Smart Card Logon for SSH
2 · About SSH and Smart Card support (RHEL 7)
Do the Disney Infinity characters use NFC to communicate with the base? If so, could I use the .
Most of the cards are read-only and do not need this step. If your card is issued by the third party (a government), you already have pre-generated keys and certificates and you can skip this section. See moreConnecting using public key in SSH requires the presence of the public key on the server to verify clients signatures. If we don't have the public key stored separately in PEM format, we . See more
Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this .One of the authentication methods supported by the SSH protocol is public key authentication. .There are many smart cards and cryptographic devices supporting PKCS#11 interface (Cryptoki) and most of them are supported by the opensc project. This guide was tested with: SmartCard-HSM; YubiKey NEO; Gemalto Smart Card (Government PIV cards) Soft tokens
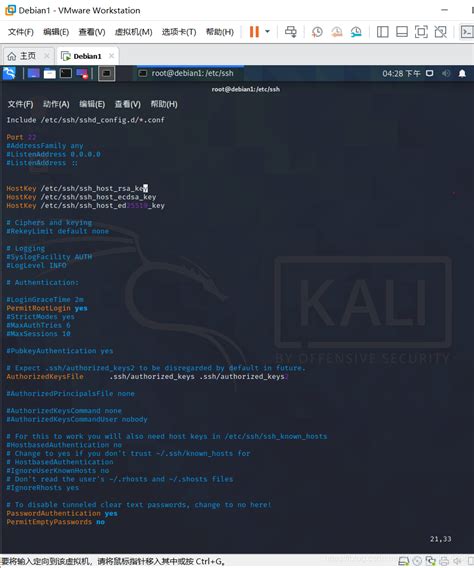
Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this guide will help you configure a .One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.
Using SSH Public Key Authentication with a Smart Card 2019-01-12. Or the result of several hours of fumbling around trying to use my new Feitian ePass Smart Card to login on my ssh server with asymmetric cryptography. Table of Content. Surely, it can't be too hard, right? Accessing the token on Windows; Creating a new key pair; Using the key .
Smart card authentication with SSH¶ One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized.If you are using your smart card to authenticate using SSH, you need to add the full certificate to the user entry in Identity Management (IdM). If you are not using your smart card to authenticate using SSH, you can add certificate mapping data using the ipa user-add-certmapdata command.
Smart card authentication with SSH
auburn live stream radio
To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need. A “smart card” is typically a plastic credit-card sized device with an IC chip. It contains a X.509 certificate and the corresponding private key for use with authentication. Ubuntu, along.
This section describes what a smart card is and how smart card authentication works. It describes the tools that you can use to read and manipulate smart card content. It also provides sample use cases and describes the setup of both the IdM server and IdM client for smart card authentication.One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.There are many smart cards and cryptographic devices supporting PKCS#11 interface (Cryptoki) and most of them are supported by the opensc project. This guide was tested with: SmartCard-HSM; YubiKey NEO; Gemalto Smart Card (Government PIV cards) Soft tokens
Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this guide will help you configure a .One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.
auburn basketball radio mobile al
Using SSH Public Key Authentication with a Smart Card 2019-01-12. Or the result of several hours of fumbling around trying to use my new Feitian ePass Smart Card to login on my ssh server with asymmetric cryptography. Table of Content. Surely, it can't be too hard, right? Accessing the token on Windows; Creating a new key pair; Using the key . Smart card authentication with SSH¶ One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized.If you are using your smart card to authenticate using SSH, you need to add the full certificate to the user entry in Identity Management (IdM). If you are not using your smart card to authenticate using SSH, you can add certificate mapping data using the ipa user-add-certmapdata command.To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need.
A “smart card” is typically a plastic credit-card sized device with an IC chip. It contains a X.509 certificate and the corresponding private key for use with authentication. Ubuntu, along.This section describes what a smart card is and how smart card authentication works. It describes the tools that you can use to read and manipulate smart card content. It also provides sample use cases and describes the setup of both the IdM server and IdM client for smart card authentication.
Smart Card Logon for SSH
auburn football on xm radio
The ACR1255U-J1 ACS Secure Bluetooth® NFC Reader combines the latest 13.56 MHz contactless technology with Bluetooth® connectivity for on-the-go smart card and NFC .
ssh smart card device|About SSH and Smart Card support (RHEL 7)