rfid cannot scan tag protected by secret key Tags which do not make use of password-protection or over-the-air (OTA) encryption can have their data banks copied into new tags. RFID tags (at least Class 1 . Via Twitter, Nintendo says the NFC reader/write accessory for Nintendo 3DS and Nintendo 2DS will release on October 2, 2015. . Nintendo announced the NFC reader adapter last year, and we haven .
0 · rfid not working
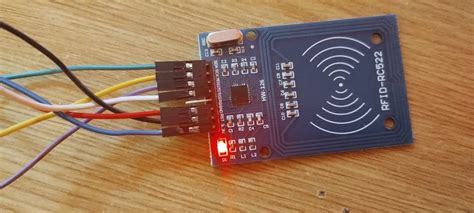
1 · rfid antenna not working
2 · rfid and privacy issues
Friday August 16, 2024 12:45 pm PDT by Juli Clover. With the launch of iOS 18.1 .
Tags which do not make use of password-protection or over-the-air (OTA) encryption can have their data banks copied into new tags. RFID tags (at least Class 1 .
Tags which do not make use of password-protection or over-the-air (OTA) encryption can have their data banks copied into new tags. RFID tags (at least Class 1 . 1. Metallic materials are interfering with the operation of the RFID reader or RFID/NFC chip. If the RFID reader is attached to a metal housing or if it lies on a metallic .
RFID systems are extremely reliable; some enterprises achieve a 99.9% system reliability on their RFID network, but what happens when an RFID system is performing .
If a generic naive RFID system is used, anyone can read, without restriction, the connection between the product and the tag and obtain information regarding the tagged . Researchers have designed an RFID chip that prevents so-called side-channel attacks, which analyze patterns of memory access or fluctuations in power usage when a .RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by .
When the tag sends its serial number to the reader, the latter requests the unique cryptographic key, which cannot be cloned. A transaction is only authorized if the correct key is received. The private key is stored in the protected memory of the RFID chip and cannot be read from outside. The reader verifies the validity of this digital signature using the public key . If it is a basic data providing tag, then it can be cloned. If it is a secure tag, it is far more difficult. For secure cards used for payments and authentication, a private key is loaded .
Compared to a simple cleartext password, this means that a passive eavesdropper can't discover the shared key. As with the password, the authentication state may be used to . Tags which do not make use of password-protection or over-the-air (OTA) encryption can have their data banks copied into new tags. RFID tags (at least Class 1 . 1. Metallic materials are interfering with the operation of the RFID reader or RFID/NFC chip. If the RFID reader is attached to a metal housing or if it lies on a metallic . RFID systems are extremely reliable; some enterprises achieve a 99.9% system reliability on their RFID network, but what happens when an RFID system is performing .
If a generic naive RFID system is used, anyone can read, without restriction, the connection between the product and the tag and obtain information regarding the tagged . Researchers have designed an RFID chip that prevents so-called side-channel attacks, which analyze patterns of memory access or fluctuations in power usage when a .
rfid not working
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by .When the tag sends its serial number to the reader, the latter requests the unique cryptographic key, which cannot be cloned. A transaction is only authorized if the correct key is received. The private key is stored in the protected memory of the RFID chip and cannot be read from outside. The reader verifies the validity of this digital signature using the public key . If it is a basic data providing tag, then it can be cloned. If it is a secure tag, it is far more difficult. For secure cards used for payments and authentication, a private key is loaded .
tsb visa debit card contactless
td bank activate contactless card
rfid antenna not working

rfid and privacy issues

$25.79
rfid cannot scan tag protected by secret key|rfid not working