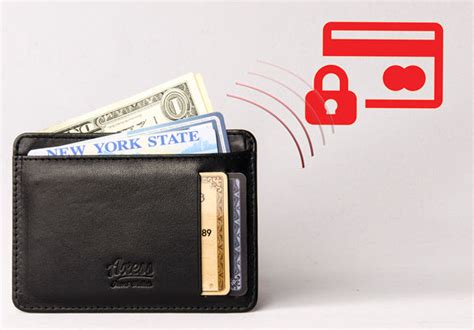
how critical is rfid protection RFID blocking tools claim to protect users against identity theft by stopping criminals from scanning your passport’s ID chip by just rubbing shoulders with you. In practice, however, RFID blocking does little to help in the most likely identity theft scenarios. The LG user manual thoroughly covers the ins and outs of the Rebel 4 to utilize core functionality like calls, texts, photography, apps and more. With the right introduction provided here, the LG Rebel 4 offers an affordable gateway into .
0 · why use rfid blocking wallet
1 · why rfid blocking wallet
2 · why rfid blocking is bad
3 · what makes something rfid blocking
4 · rfid scam
5 · is rfid blocking a scam
6 · are rfid wallets necessary 2022
7 · are rfid blocking products worthless
Click the "Get Started" button. Type "Duke" in the search box then click on Duke University. Click on eAccounts Portal. Click "Continue to Sign in" and enter your NET ID and Password. Click "Add to Wallet." Click "Add to Google Wallet." .
RFID blocking tools claim to protect users against identity theft by stopping criminals from scanning your passport’s ID chip by just rubbing shoulders with you. In practice, however, RFID blocking does little to help in the most likely identity theft scenarios.Passports and some credit cards have RFID chips that allow information to be read wirelessly. .
readid nfc demo
RFID blocking tools claim to protect users against identity theft by stopping criminals from scanning your passport’s ID chip by just rubbing shoulders with you. In practice, however, RFID blocking does little to help in the most likely identity theft scenarios. Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming". RFID is used throughout many industries to streamline processes. The revolutionary “tap-to-pay” method that has become so popular for transactions is a prime example of RFID. RFID is also how your information pops up on the screen after a customs worker scans your passport. In terms of scanning, RFID functions similarly to a bar code or QR .
One of the most critical standards for RFID is ISO/IEC 18000, which covers air interface communications for RFID in various frequency ranges. Key ISO/IEC Standards for RFID: ISO/IEC 18000-63 (UHF RFID) : The most widely used standard for passive RFID systems operating in the 860-960 MHz UHF band.
android app nfc reader
Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement authentication mechanisms to ensure that only authorized tags and readers can interact with each other. Faraday bags provide an electromagnetic barrier that shields devices from all signals, creating a reliable defense against digital intrusion. This level of protection is critical in high-security environments where unauthorized tracking or hacking could lead to severe breaches of information or privacy. Unlike RFID blockers, Faraday bags ensure .To reduce these risks, implementing strong security measures is crucial. This includes encrypting RFID data to protect it during transmission, using authentication protocols to verify user access, and regularly updating security software to defend against potential threats. Discover what RFID blocking is and how it protects your personal information from theft and unauthorized access. Stay safe with RFID blocking technology!
phone says can't read nfc tag
RFID for supply chain management (SCM) plays a critical role in connecting the physical world with management systems; RFID collects data to be analyzed and improves
The best way to prevent eavesdropping is to adopt a layered security approach that prioritizes encryption and secure authentication protocols. Managers should ensure every RFID system within the supply chain uses end-to-end encryption to protect transmitted data. RFID blocking tools claim to protect users against identity theft by stopping criminals from scanning your passport’s ID chip by just rubbing shoulders with you. In practice, however, RFID blocking does little to help in the most likely identity theft scenarios. Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming". RFID is used throughout many industries to streamline processes. The revolutionary “tap-to-pay” method that has become so popular for transactions is a prime example of RFID. RFID is also how your information pops up on the screen after a customs worker scans your passport. In terms of scanning, RFID functions similarly to a bar code or QR .
One of the most critical standards for RFID is ISO/IEC 18000, which covers air interface communications for RFID in various frequency ranges. Key ISO/IEC Standards for RFID: ISO/IEC 18000-63 (UHF RFID) : The most widely used standard for passive RFID systems operating in the 860-960 MHz UHF band.
Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement authentication mechanisms to ensure that only authorized tags and readers can interact with each other.

Faraday bags provide an electromagnetic barrier that shields devices from all signals, creating a reliable defense against digital intrusion. This level of protection is critical in high-security environments where unauthorized tracking or hacking could lead to severe breaches of information or privacy. Unlike RFID blockers, Faraday bags ensure .To reduce these risks, implementing strong security measures is crucial. This includes encrypting RFID data to protect it during transmission, using authentication protocols to verify user access, and regularly updating security software to defend against potential threats.
why use rfid blocking wallet
why rfid blocking wallet
Discover what RFID blocking is and how it protects your personal information from theft and unauthorized access. Stay safe with RFID blocking technology! RFID for supply chain management (SCM) plays a critical role in connecting the physical world with management systems; RFID collects data to be analyzed and improves
why rfid blocking is bad
read dog chip with nfc
nfc tag reader iphone xr
NFC Tools is an app which allows you to read, write and program tasks on your NFC tags and other compatible NFC chips. Simple and intuitive, NFC Tools can record standard information on your NFC tags which will be .
how critical is rfid protection|are rfid wallets necessary 2022